What is Authentication & Security?
Authentication and security controls determine which systems can connect, which records they can access, what actions they can perform and how activity is logged. This is especially important where integrations touch tenant, landlord, client, finance or compliance records.
How it works in a Proplix-connected environment
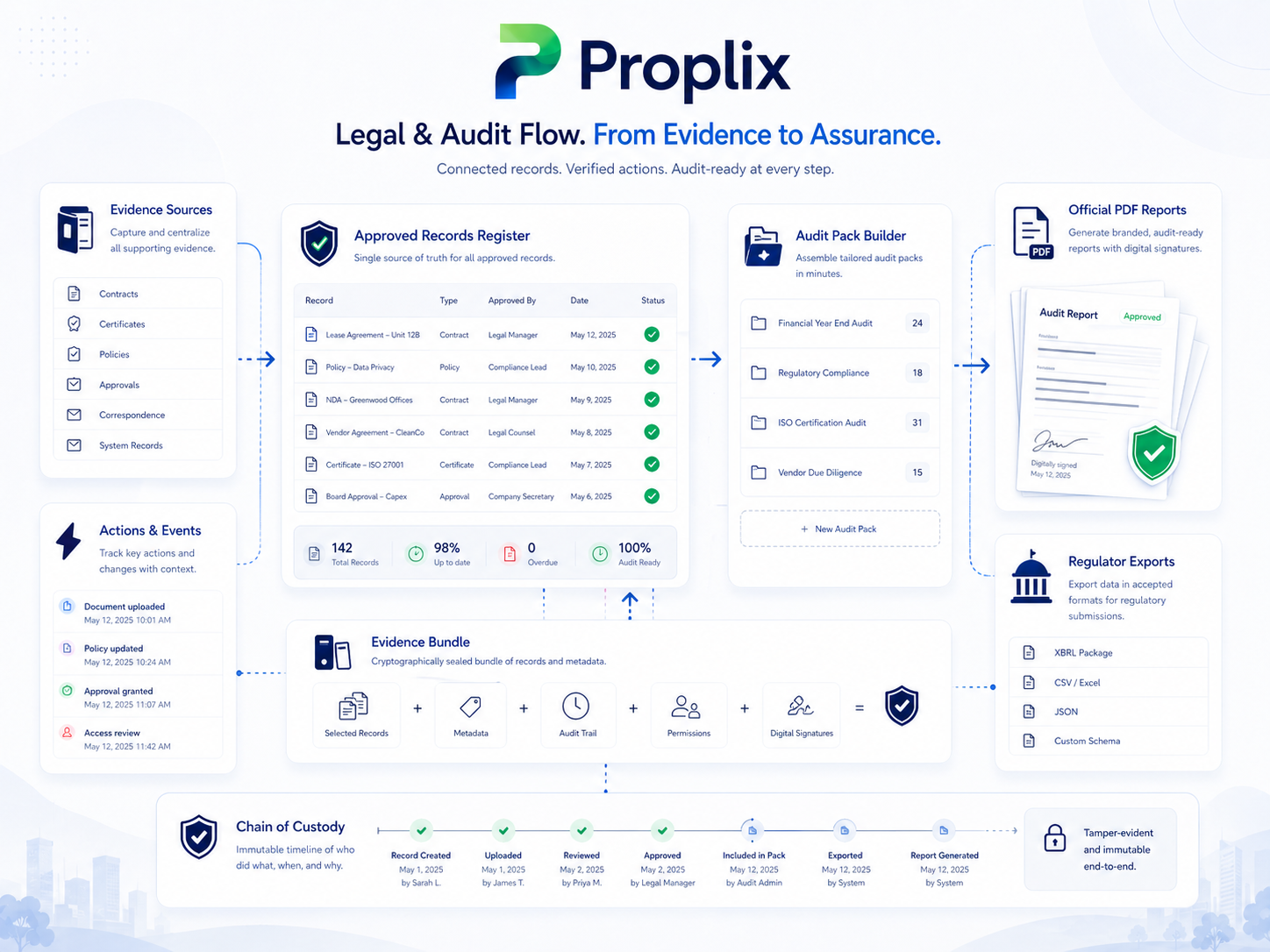
Proplix treats integration as an operational workflow, not just a technical connection. The aim is to keep property, people, compliance, finance, maintenance and reporting information moving with context, ownership and audit visibility.
- Define the integration actor, application or external service.
- Apply suitable authentication and permission boundaries.
- Limit access to the records and actions required for the use case.
- Log important activity for operational review.
- Review access periodically and remove unused integration routes.
How Proplix supports customisation
Proplix security planning can be customised around user roles, departments, offices, property portfolios, approval managers, external partners, data retention rules, compliance modules and audit reporting requirements.
Typical integration opportunities
- Role-based API access planning
- Secure webhook endpoint rules
- Limited-scope connector credentials
- Audit trails for integration actions
- Data minimisation and controlled record exposure
- Support handover and access review process
Professional implementation note
Every integration should be scoped, tested and documented before it becomes part of live operations. Proplix pages describe the business workflow and integration design principles, while final technical implementation depends on the external system, available API access, security requirements and agreed customisation plan.